March 14, 2016
With the recent launch of CCS’ #FindThePhish Twitter contest, it is a great time to delve deeper into the murky waters of phishing, and explore the potential impacts of phishing on individuals as well as on an organization.
On an average day, the University of Guelph receives 3-4 million email messages. An astounding 93% of those emails are identified as phishing attempts or SPAM before they even reach your mailbox! But technology alone can’t solve all of our problems. We rely on YOU – the end user – to be aware of what to look for and to make educated decisions when reviewing your email. If these harmful emails are not recognized, the potential impact can be significant, especially when cyber criminals gain access to staff accounts with from which they can access University systems and data.
Is phishing really that dangerous? What could possibly go wrong? And why should I be concerned?
If you provide your U of G credentials to a site other than the University of Guelph (i.e., if you get tricked into a phishing scam), your username and password are now in the hands of a third party with malicious intent. They could sell that information, or use it to access your data, and make use of your access in other ways. This could include access to your email, access to your pay information, access to University systems, or access to University files and applications. And if you have used the same password on your U of G account as other internet sites, such as online banking or social media, the impact can expand very quickly. These are smart people who know how to make the most of what you’ve given them.
Potential impacts could include:
- Loss of personal information (email conversations, photos, private information)
- Financial loss and credit score tampering
- Identity theft or impersonation
- Further spread of malware or phishing email
- Unauthorized access to University systems
- Access or breach of University data
- Loss of productivity due to locked account or need to investigate
The impacts of phishing are well documented, with almost daily news stories detailing phishing attacks and their subsequent fallout. Here are just a few examples of recent news articles showing the impact that phishing emails can have on an organization:
- January 25 2016 - Phishing Email Leads to Data Breach at University of Virginia (https://www.helpnetsecurity.com/2016/01/25/phishing-email-leads-to-data-breach-at-university-of-virginia/ [1])
- February 3 2016 - Magnolia Health Corporation Reported That All Active Employees Were Exposed After an Excel Spreadsheet Containing Sensitive Employee Data was Sent to a Person Posing as the Company's CEO (http://www.hipaajournal.com/magnolia-health-victim-of-email-spoofing-phishing-scam-8314/ [2])
- February 29 2016 - Snapchat Suffers Employee Data Breach after Phishing Attack (http://www.newsfactor.com/news/Snapchat-Suffers-Phishy-Data-Breach/story.xhtml?story_id=00100018PO9K [3])
- March 6 2016 - Seagate Phish Exposes All Employee Tax Documents - https://krebsonsecurity.com/2016/03/seagate-phish-exposes-all-employee-w-2s/ [4]
What Can I Do to Protect Myself?
- Recognize the signs of a phishing email. Read our write-up on how to spot a phishing scam - https://www.uoguelph.ca/ccs/news/do-you-know-how-recognize-phishing-scam [5]
- Take the Phishing Quiz [6] to test your knowledge.
- Check the Scams List first. Keep an eye on the CCS Information Security ‘Recent Scams and Phishing Attempts’ page (https://www.uoguelph.ca/ccs/recent-scams-and-phishing-attempts [7]) or Subscribe for Scam Notifications on that page. If you suspect a phishing attempt, don’t click any links!! Check our page first or contact the CCS Help Centre for direction (see contact info below).
- Ask for help. The CCS Help Center is just an email or phone call away for questions regarding phishing emails. Email them at 58888help@uoguelph.ca [8] or call 519-824-4120 x58888.
- Share your knowledge! Participate in our #FindThePhish Twitter contest - https://www.uoguelph.ca/ccs/findthephish-twitter-contest [9]
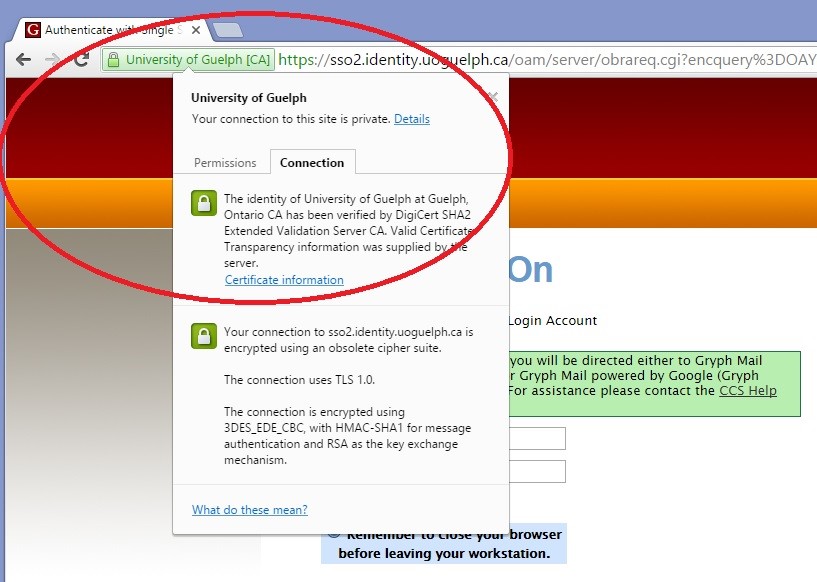
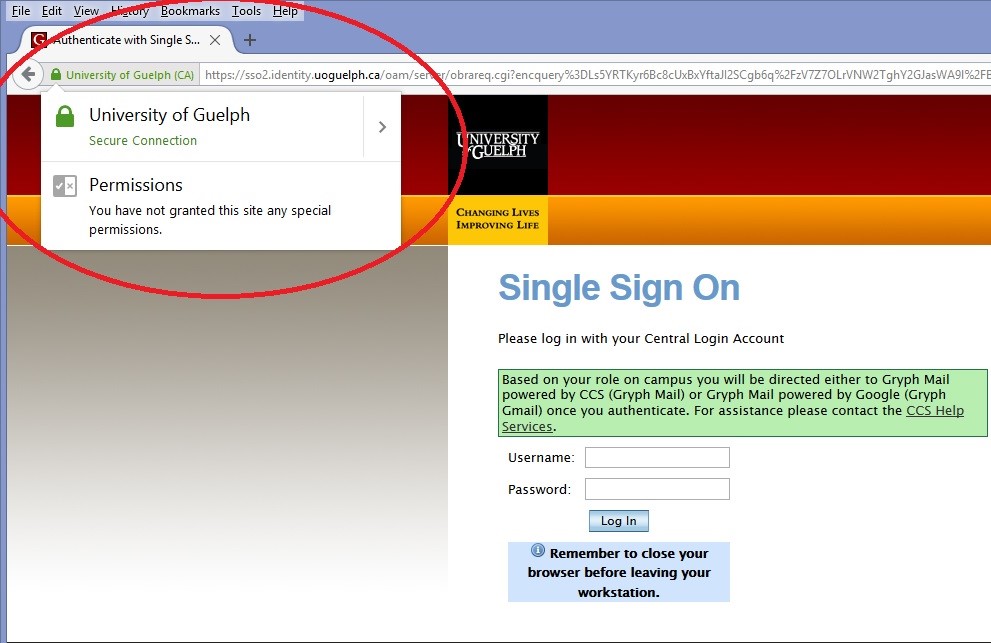
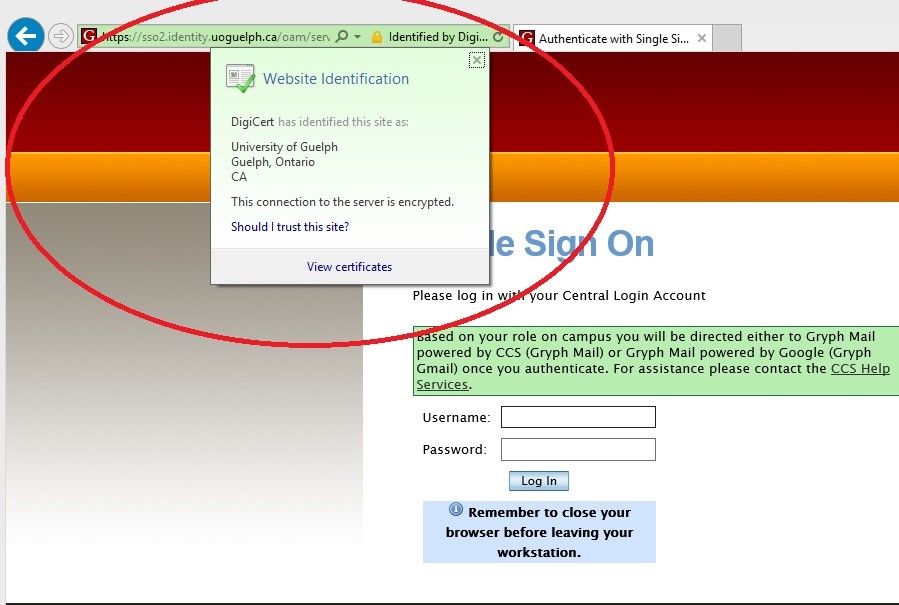
- Know how to spot a fake login page. Always remember that the University of Guelph will never ask you to reveal your ID and password by email, and you should always verify the validity of a site that asks for this privileged information. Below are screen captures from Chrome, FireFox, and Internet Explorer when visiting the University of Guelph Single Sign-On site. By clicking on the lock icon in the address bar, you can verify that the site is truly owned by the University of Guelph and not an imposter.
Written by: Stephen Willem (Manager, CCS Information Security)