July 11th, 2016
In a throwback to the late 90s and early 2000s, attackers have added a particularly old tool to their arsenals. Researchers have seen an alarming uptick in the number of macro based malware. Back in the day people used macros in office documents to automate certain tasks. They largely fell out of favour do to security implications but just like Pokémon, they are back with a vengeance.
Some attachment names we have seen imitate invoices, receipts, and other important documents, for example:
- case number.doc
- e-ticket_79010838.doc
- fax_msg896-599-5459.doc
- invoice_723961.doc
- legal_complaint.doc
- logmein_coupon.doc
- receipt_3458934.doc
Macro malware was fairly common several years ago because macros ran automatically whenever you opened a document. However, in recent versions of Microsoft Office, macros are disabled by default. This means malware authors need to convince you to turn on macros so that their malware can run. They do this by showing you fake warnings when you open a malicious document. An example of this is shown below:
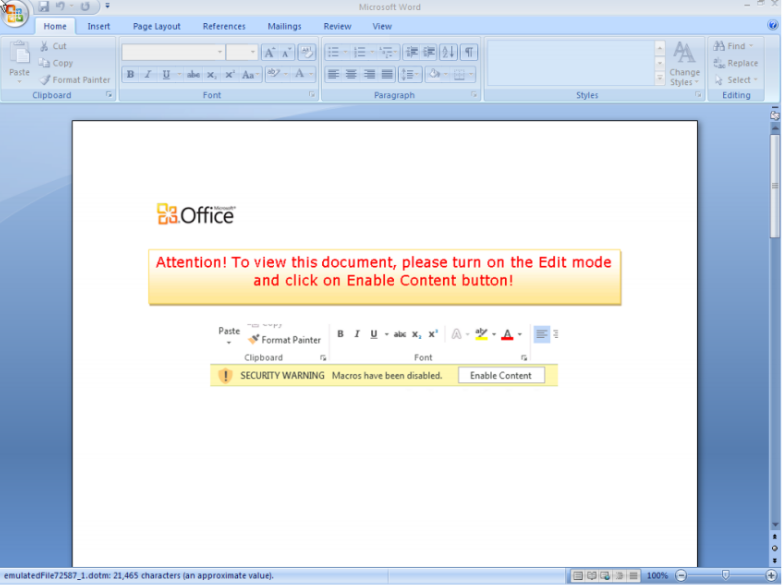
If you follow these prompts and enable macros, the malware can run.
In order to prevent yourself from a macro based attack:
- Disable Macros in your MS Office programs.
- Never open unsolicited attachments in emails.
- Always keep your system and antivirus up-to-date.
- Regularly backup your files on an external hard-drive just in case.
Written by: Chris Sowley (Cyber Forensics Analyst, Information Security)