Search related to Phishing

March 24, 2017
We’ve all received phishing emails asking us click a link to reset our password, or to reply to an email with our login information to stop our accounts from being closed, etc. These emails are lazily sprayed to hundreds or thousands of people at a time, with the hopes that someone will reply, ensnaring another account they can use to spread more spam out.
February 1, 2017
Cybercriminals know the best strategies for gaining access to your institution’s sensitive data. In most cases, it doesn’t involve them rappelling from a ceiling’s skylight and deftly avoiding a laser detection system to hack into your servers; instead, they simply manipulate a community member.
October 20, 2016
When an IT change takes place at the University of Guelph, hackers are more active. For example, in the summer of 2016, when the University transitioned the staff email system to the new Gryph Mail Office 365, there were renewed attempts to lure our users with phishing emails containing links to an illegitimate login page.
April 4, 2016
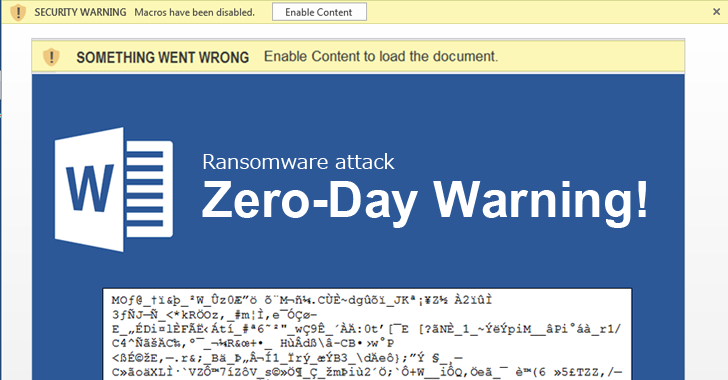
You may not realize it, but you are a phishing target at school, at work, and at home. Ultimately, you are the most effective way to detect and stop phishing scams. When viewing e-mail messages, texts, or social media posts, look for the following indicators to prevent stolen passwords, personal data, or private information.

March 14, 2016
With the recent launch of CCS’ #FindThePhish Twitter contest, it is a great time to delve deeper into the murky waters of phishing, and explore the potential impacts of phishing on individuals as well as on an organization.